Does your business take old tech disposal seriously? If not, your business data is at serious risk..
With the average lifespan of most end user devices such as laptops/desktops/tablets being 4 years, and mobile phones just 2.5 years, a lot of tech comes and goes through your business in a short period of time.
With the amount of confidential information that our devices store, it is crucial that you have an end-of-life process in place for your old technology.
Sadly, if your process is to simply delete the files from your old IT gear and then turf them in the bin, then sooner or later your sensitive business information will become public.
Believe it or not, there is a thing called ‘Dumpster Diving Attacks’. Dumpster Diving has been around for years, and is where people go through your industrial bins, hard rubbish and even waste transfer stations searching for old IT gear.
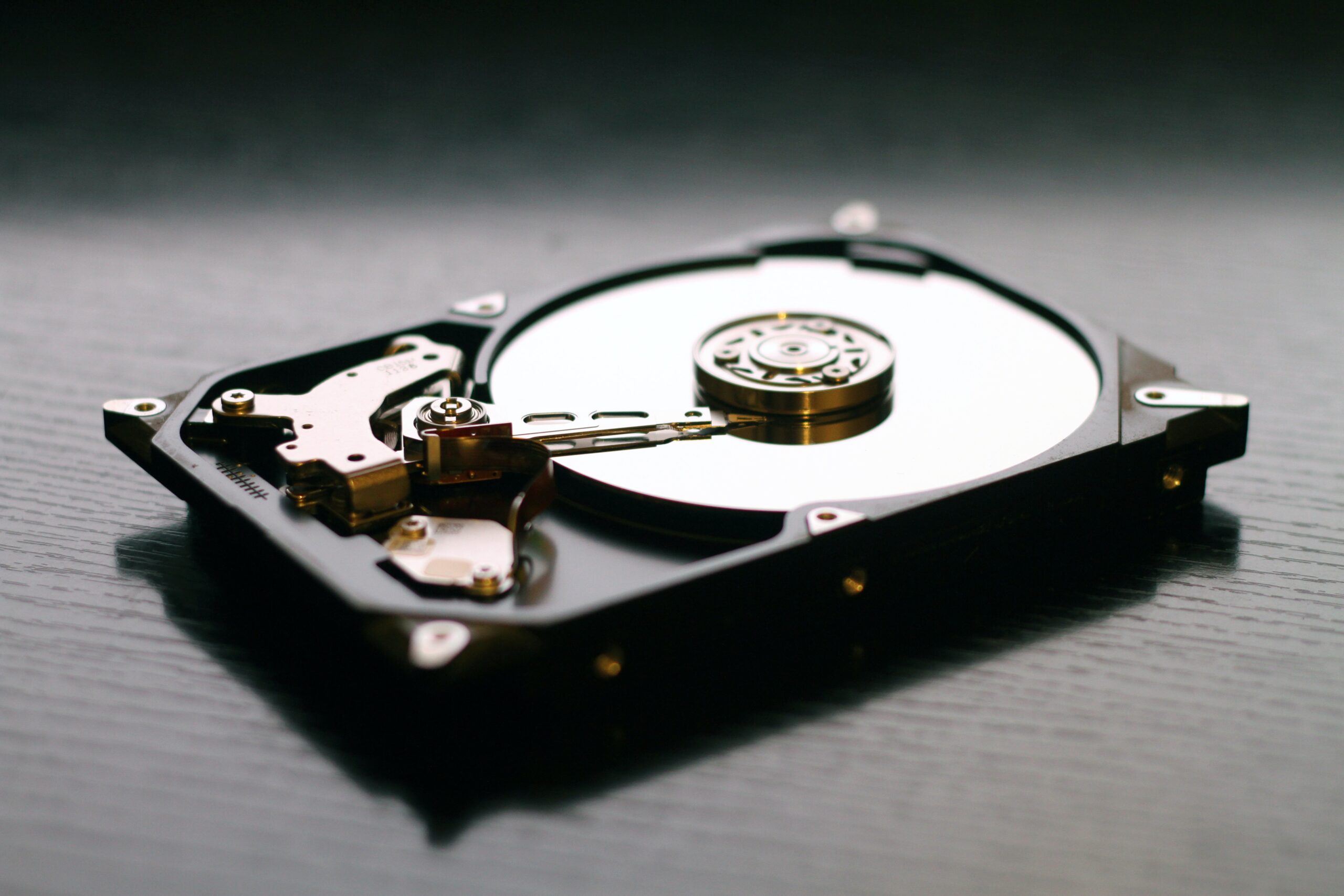
The Dumpster Divers will then remove hard drives and using specialised software scour them for sensitive business information that can be used to extort money from unsuspecting business owners.
It is one of the easiest hacks to perform and often a very lucrative one for the perp.

So, when it comes time to get rid of the old and replace with the new, what do you need to do prior to disposing of your old gear?
Here are a few quick tips to keep your information safe.
- Backup up any data you want to keep.
- Transfer any authentication applications such as Google Authenticator / Microsoft Authenticator / Authy.
- Remove any portable media such as SIM cards, USBs, SD Cards, DVDs
- Remove any company identifiers such as company logos, asset stickers, name tags so on.
- Perform a secure erase of any hard drives or storage devices.
Don’t fall in the trap of doing a quick erase or format of the disk. Perform a secure erase (which takes several hours) or better yet use the services of a secure data destruction service that guarantees your data in properly disposed. - Be environmentally friendly and dispose of it via eWaste at your local waste transfer station.
The easily forgotten.
Secure data disposal does not just apply to Servers, Computers, phones and tablets. You need to make sure that you are also securely erasing:
- Network equipment (switches/routers/WAPS)
- NAS and storage devices
- External Hard drives
- DVDs & USB sticks
- Photo Copiers
- Old Phone systems.
*** Important note ***
Photocopiers are a treasure trove of data. Most copiers have an internal hard drive that keeps a copy of scanned documents. Don’t fall into the false sense of security thinking that your photo copier provider will securely erase the internal drives when you return their device.
Put simply, any system that you use that has sensitive company data on it needs to be considered.
Still confused? Don’t be, reach out to the team at Runtime and we can work with you to put processes in place to keep your team secure.