What’s the deal with 2FA?
In the big bad world that we live, you must protect yourself and more importantly you must protect your company and the privacy of your clients. Stealing a company’s data or breaching security is big business for hackers and can wreak havoc on your business and its reputation.
The most common cause of security compromise for accounts is weak passwords or the same password used on multiple accounts.
If you have spent any time talking to an IT technician, you will no doubt have heard them tell you to use 2FA or MFA.
So, what exactly is 2FA/MFA and why do you need it?
2FA / MFA
2FA stand for Two-Factor Authentication and MFA stands for Multi-Factor Authentication.
Essentially, 2FA/MFA is an additional verification that is required on top of your username and password to log into an account – this adds an additional layer of security that can help cut down on potential security breaches and automated attacks.
2FA/MFA comes in a variety of methods such as
- SMS/Text message to a trusted device
- A verification code to a trusted email account
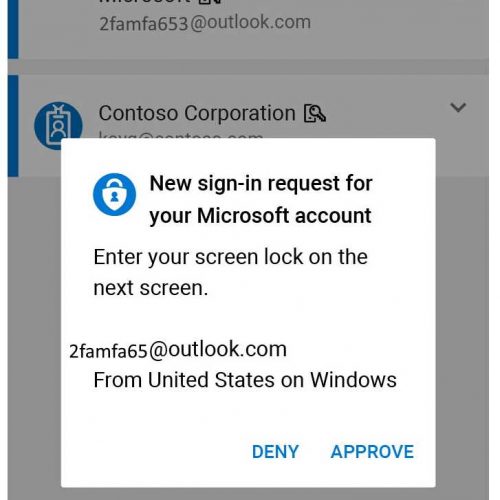
- A verification via an app like Google Authenticator / Microsoft Authenticator
- Use of a hardware device such as YubiKey
Why do I need MFA?
Gone are the days when you could rely on just a username and complex password to secure your account. Nowadays hackers have a plethora of tools available to run automated attacks and attempt to gain access to your accounts. These attacks are happening 24/7 365 days a year.
If they do manage get into your account, there is usually a threat of ‘Pay me this much or I will delete your data, leak your clients data or lock your account’.
Sadly, in the age of the internet and global business you are not dealing with people who are reasonable and have the same morals as you. You are dealing with people who are happy to extort the vulnerable and would sell their grandmother for a few dollars.
How does 2FA/MFA work?
Traditional Non-MFA Account login
- You visit your mail provider or software site (Google, Office 365, Accounting package so on)
- You type in your username or email address
- You type in your password and click login
- Your request to login is processed and you now have access to your email/collaboration suite/software
MFA Account login
- You visit your mail provider or software site (Google, Office 365, Accounting package so on)
- You type in your username or email address
- You type in your password and click login
- You will be prompted for either a verification code or to approve your login via a trusted device or app.
- You type in the additional verification and then you be logged in as per normal
So, now that you know the basics what method of MFA is best for you? Only you can decide this, however a few things to keep in mind
- SMS/Text message – this provides some extra security however, SMS/Text messages are relatively easy to compromise
- Email verification to trusted account – This is a better option, however that account must be secured correctly.
- Google Authenticator / Microsoft Authenticator apps – These are a much safer option as they provide one-time dynamic keys and are generally installed on a trusted device.
- YubiKey – This is a special USB or Near-field device that when plugged in or in the proximity of your computer allows login. YubiKey is one of the best options but it comes at a monetary cost and if you have lots of employees then it will become cumbersome to manage.
For ease of use, flexibility and practicality Google Authenticator / Microsoft Authenticator are a very good starting point, this will dramatically reduce your chances of compromise and better yet, most software suites and accounting packages support Google/Microsoft Authenticator.



